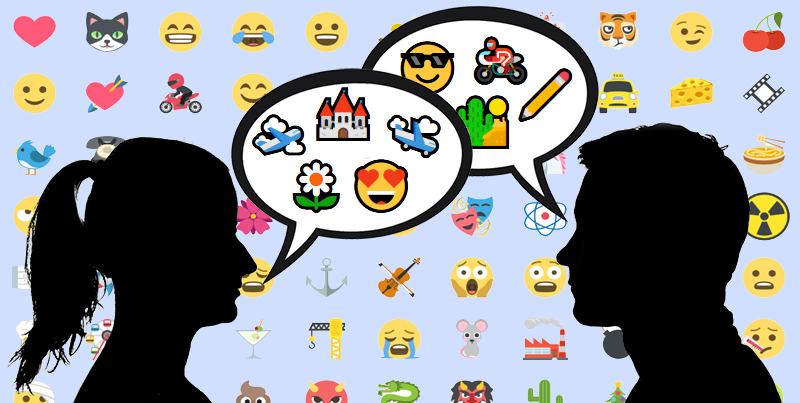
We all get them, especially around the holidays: those emails with little pictographs in the subject line. At Halloween, they are jack-o-lanterns and ghosts (🎃, 👻), further into winter they might be snowmen or Christmas trees (☃, 🎄). Sometimes they relate to the sender’s industry. Guitar Center, for instance, regularly uses the guitar pictograph (🎸), while Webdesigner News starts every subject line with the image of a pencil (✏). These are emojis, and have become popular tools for spicing up subject lines to make them more appealing. In this article we’ll take a look at the pros and cons of using emojis, and things to look out for when using them.
Emoji or Emoticon?
First let’s get the out of the way the inevitable question, “What is the difference between an emoji and an emoticon?” An emoticon is a facial expression created using the limited assortment of punctuation that is available in basic English text. The most well-known example is the colon and right parenthesis indicating a smiling face: :) . The alternative to basic text is Unicode, a character coding system designed to include every character in every language. In Unicode, there is an emoji for a smiling face (☺), along with a large assortment of other tiny pictographs. Unlike a smiling face created with a colon and a right parenthesis, the emoji is one character, not two. There are several emojis you can choose from to indicate various levels of mirth (😄😃😀😊😁), along with characters for nearly every other human emotion (😯😨😭😡😳).
Emojis got their start on Japanese mobile phones, where they were used to replace emoticons. Although the names sound similar, the word emoji has nothing to do with emotions. It is a combination of the Japanese words for “picture” (e – 絵) and “character” (mo-ji – 文字).Their worldwide acceptance began when Apple decided to include emojis as a feature on its iPhones in 2009. Then in 2010, hundreds of emojis were encoded and introduced in the Unicode Standard, and more are added every day. As of this writing, there are 722 emojis available with Unicode character coding. Emojis have popped up everywhere from Android phones to Gmail.
As befitting their Japanese roots, some emojis are specifically aimed at Japanese culture and leave westerners scratching their heads. Emojis for foods such and Dango (🍡) and Oden (🍢), and festivals such as Tanabata (🎋) and Tsukimi (🎑) presumably don’t see much use in America and Europe, while other symbols, such as the white flower (💮) might be used, but in an entirely different context from how it’s used in Japan (in Japan it is used to mean “well done”).
Where Are They?
Unless you are using an iPhone to write your mailings, which is highly doubtful, finding the emojis on a keyboard can be tricky. You can type in the Unicode directly, but that is a pain in the neck, and you first have to know these codes to type them. For instance, to add an airplane (✈) to your subject line, you’d need to type in U+2708 (hold down the Ctrl+Alt+Shift keys, type U, type 2708, then hit enter). It’s a lot of work for one character, and it doesn’t always work anyway. Some desktop systems have shortcuts for inserting emojis, or special pull-down menus, but these are still slow. The easiest way to add emojis that we’ve found is iEmoji.com, which lets you compose the subject line on their web page, then copy and paste it to your email marketing software. But some care should be taken when doing this, which leads us to the next point: Why do some emojis work in subject lines and others don’t?
Question Marks and Empty Squares
Have you tried using emojis in your subject lines, only to have them replaced by small squares or questions marks? There are two primary causes for this. The first is that you are using a newer, unusual emoji that is not included across all systems. The country flags, for instance, do not show up in most email reader subject lines, and often not in the content either. In most email readers, the newer ability to choose the skin tones of certain emojis isn’t available, and will add blank squares or question marks to a subject line (more on this below). When using emojis in the subject line, it is safest to stick to the default emojis, which usually appear in yellow.
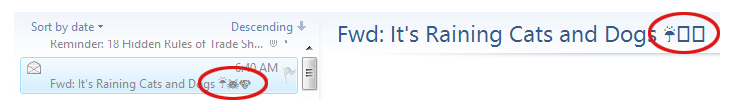
With a few email readers, such as Live Mail, how it displays can even depend on where it is in the software. Take this example:
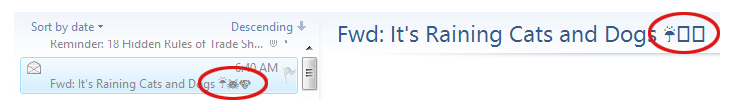 All three emojis appear in the list window on the left, but not in the title window on the right. The first emoji (the umbrella) appears correctly in both areas, while the others (the cat and dog) appear as empty boxes on the right. The reason for this is because the umbrella is one of the original emojis that were introduced in 1995. As a rule, these will appear in your subject lines more often than the newer emojis will. Some of these characters, such as the smiley face (☺), musical notes (♪ ♫), and card suits (♠ ♣ ♥ ♦) were added early on, and are available as symbol characters in basic English character sets.1 Here is a list of the original 1995 emojis:
All three emojis appear in the list window on the left, but not in the title window on the right. The first emoji (the umbrella) appears correctly in both areas, while the others (the cat and dog) appear as empty boxes on the right. The reason for this is because the umbrella is one of the original emojis that were introduced in 1995. As a rule, these will appear in your subject lines more often than the newer emojis will. Some of these characters, such as the smiley face (☺), musical notes (♪ ♫), and card suits (♠ ♣ ♥ ♦) were added early on, and are available as symbol characters in basic English character sets.1 Here is a list of the original 1995 emojis:
☺ ☹ ☠ ☝ ✌ ✍ ❤ ❣ ♨ ✈ ⌛ ⌚ ☀ ☁
☂ ❄ ☃ ☄ ♠ ♥ ♦ ♣ ☎ ⌨ ✉ ✏ ✒ ✂
☢ ☣ ↗ ➡ ↘ ↙ ↖ ↕ ↔ ↩ ↪ ✡ ☸ ☯
✝ ☦ ☪ ☮ ▶ ◀ ☑ ✔ ✖ ✳ ✴ ❇ ‼ 〰
♈ ♉ ♊ ♋ ♌ ♍ ♎ ♏ ♐ ♑ ♒ ♓
© ® ™ Ⓜ ㊗ ㊙ ▪ ▫
A second, and more likely cause of question marks in the subject line, is that your email is set to something other than Unicode. If the character you want to use is not available in the character set you are using, it will not appear in the subject line. Go to the settings while in your email marketing software and check the character encoding choice. If it doesn’t say “UTF-8” it’s probably not going to work in the subject line, even if it works in the content.
As a rule, it is never a good idea to use emojis to replace words in a subject line. If the emoji is replaced with a question mark, you might end up with a subject line that still makes sense, but says something you don’t want it to. For instance, if you replaced the word “love” with a heart in the subject line “You’ll ❤ our deals,” you could end up with this: “You’ll ? our ideas,” which isn’t exactly a confidence builder, and could be read as “You’ll question our deals.” In fact, a scan of various emails—and even web pages—shows that using the heart symbol to replace the word love might just be the number one gaffe. I even found the following line in an online article about emojis: “There’s a lot of ? for emoji these days….”
It is safer to put the emojis at the beginning and the ends of the subject lines, or as breaks between words. Even so, you should ask yourself: If a question mark appears instead, will it affect the subject line’s meaning?
I’m Not Mad, I’m Happy
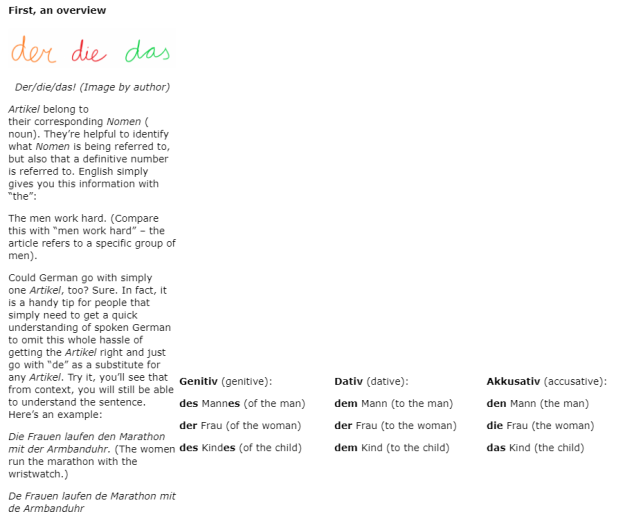
In some cases, the emojis from one operating system are different enough from the emojis in another to cause confusion. Here, for instance is the emoji labeled “drooling face”:
 Two appear happy, two appear unhappy, and the last one looks downright scared. One doesn’t even appear at all. While it is unusual for emojis to vary this much across platforms, it doesn’t hurt to check the emoji you plan to use to make sure it doesn’t change too drastically when viewed on different devices and operating systems. The easiest place to do this is at the Unicode Consortium’s Full Emoji Data page. There, you’ll find all the emojis—including a few that appear animated, such as the Gmail emojis, which sometimes cry, bounce up and down, or wink. The Unicode Consortium’s Data page also lists the date when each emoji was introduced, which can help you determine how safe it is to use that emoji. An emoji introduced in 2016 is probably not going to show up in a subject line, and might not even show up in the content.
Two appear happy, two appear unhappy, and the last one looks downright scared. One doesn’t even appear at all. While it is unusual for emojis to vary this much across platforms, it doesn’t hurt to check the emoji you plan to use to make sure it doesn’t change too drastically when viewed on different devices and operating systems. The easiest place to do this is at the Unicode Consortium’s Full Emoji Data page. There, you’ll find all the emojis—including a few that appear animated, such as the Gmail emojis, which sometimes cry, bounce up and down, or wink. The Unicode Consortium’s Data page also lists the date when each emoji was introduced, which can help you determine how safe it is to use that emoji. An emoji introduced in 2016 is probably not going to show up in a subject line, and might not even show up in the content.
Politically Correct Emojis
While animation is more site specific, and doesn’t affect the individual emojis, there is another recent addition to the emojis that will affect how and emoji behaves in a subject line. After people complained that the emojis of hands and faces were not ethnically inclusive enough, a feature was added whereby you can specify the gender of an emoji and its skin color. Care must be taken when using skin tones and genders as these add additional code to each emoji. For instance, the code for the left pointing finger emoji is U+1F448, while the code for the same emoji with pale skin is U+1F448+U+1F3FB. In subject lines, even if the original default emoji appears, the gender and color information will in most cases appear as empty square blocks or question marks. For this reason, it is best to stick to the basic emojis and avoid skin tones and gender additions until more mail readers are compatible with these features.
Emojis and Deliverability
As always, the most important question is: Can emojis affect the deliverability of an email? Our tests suggest that, under some circumstances, emojis do appear to have a negative effect on an email’s deliverability, but a minor one. Mailings with large quantities of emojis in the subject line and contents were more likely to end up in the spam folder, while those that used them more judiciously appeared to have no problems getting through. Obviously a subject line that is nothing but emojis is probably not a good idea. Some spam filters can identify is a subject line is nonsense, and a string of emojis looks just like gibberish. We recommend restricting the use of emojis in subject lines to no more than three, and to make sure there is actual text in the subject line as well. Keep in mind also that there may be aspects of your content that are pushing your mailings close to a negative rating, and the emojis won’t do anything to improve the situation. For for information on what to look out for, check out our white paper, Deliverability Enhanced.
As to which emojis provide the best open rates, a quick scan of the articles that discuss this shows that there is no consensus here. In all likelihood, this data changes from month to month anyway. The only meaningful answer is to see how they do in your own tests, and proceed accordingly. Like those articles that tell you which day of the week is best for sending, any article that claims to know which emoji performs best is working from a limited data set and should be taken with a grain of salt.
Test and Test Again
If you do plan to use emojis in your subject lines, our advice is, as always with any first time format experimentation, test and test again. We would also recommend paying closer attention than usual to the deliverability results in your tests. Some A/B split testing against subject lines without emojis or with different emojis isn’t a bad idea either. Emojis can be a fun way to enliven your subject lines and increase open rates, but it will still require testing with your own recipients to see if they’ll work for you.

1. It should be noted that the term “emoji” was not applied to these character, however, until Unicode version 6.0, released in 2010.